What Are Proxy Server | Use of Proxy Server
Connecting to the Internet is not safe nowadays, they are many attacks and scams we have seen in the past, whether on PC or Mobile devices. In such cases, proxy servers might be something that can help people to stay safe from attackers and scammers.
Attacks in which IP addresses are targeted directly, proxy servers can be a simple way out, which can make our devices safe from attackers.
What Are Proxy Server?
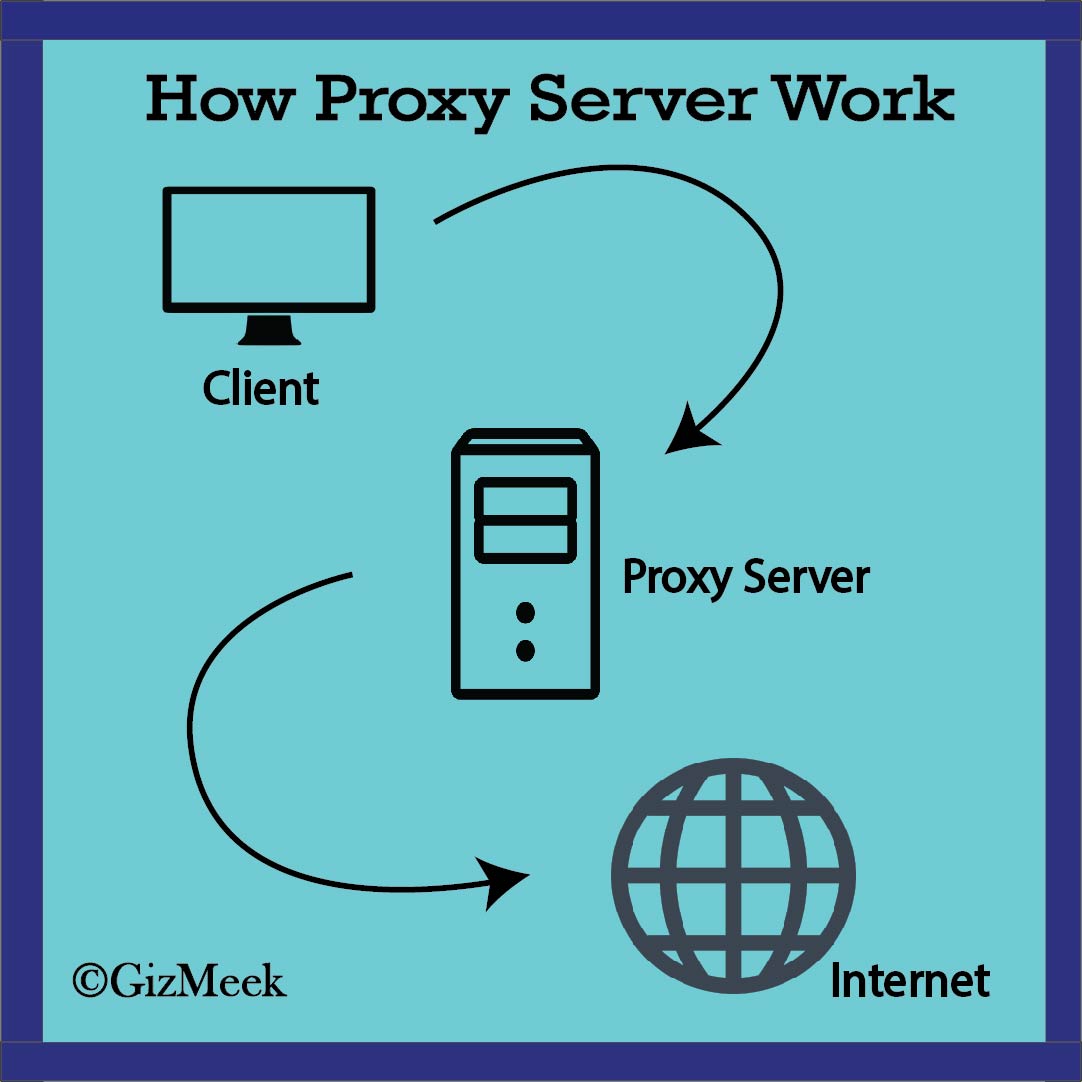
A Proxy Server sits in between client and host server, all the requests are being fetched by the proxy server and the proxy server serves the response to the client. Proxy servers provide varying levels of functionality, security, and privacy depending on your use case, needs, or company policy.
In a Proxy Server, the traffic flows through an intermediate server instead of a direct flow between you (client) and the host server.
Use of Proxy Servers
Proxy Servers offers great options:
-
Monitoring and Filtering: Proxy Servers can be used to monitor and filter all the traffic that is going through it and control it.
-
Improving performance: Performance is improved by enabling caching system on the proxy server. Any new request's response is cached and served to the client in the future if the same request is made again from the proxy server instead of going to the main host server.
-
Translation: It helps to customize the source site for local users by excluding source content or substituting source content with original local content.
-
Security: In a Proxy Server, your original public IP address is replaced with the proxy IP, hence tracking you down is quite hard.
The most common use of proxy servers can be seen in the case of torrent sites. You might have searched for various torrent site's proxy servers, such as rarbg proxy, pirate bay proxy, extra torrent proxy, in short, proxy servers can be used to access some blocked content. Proxy server working is quite similar to the VPN or Virtual Private Network that we use.
How to Use Data Saver on Android
Related post
"Create the difference and be the change you want to see."






