RockYou2021 world’s largest password leaked online with 8.4 billion entries
A list of leaked passwords discovered on a hacker forum may be one of the largest such collections of all time. A 100GB text file leaked by a user on a popular hacker forum contains 8.4 billion passwords, likely gathered from past data breaches.
By combining 8.4 billion unique password variations with other breach compilations that include usernames and email addresses, threat actors can use the RockYou2021 collection to mount password dictionary and password spraying attacks against untold numbers of online accounts.
Its 3.2 billion leaked passwords, along with passwords from multiple other leaked databases, are included in the RockYou2021 compilation that has been amassed by the person behind this collection over several years. According to the post author, all passwords included in the leak are 6-20 characters long, with non-ASCII characters and white spaces removed. The same user also claims that the compilation contains 82 billion passwords.
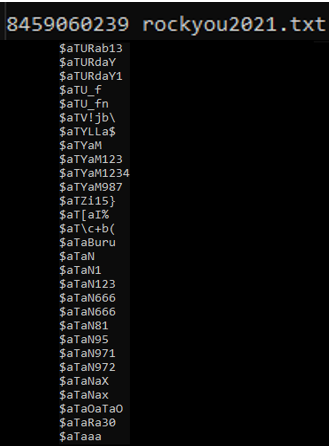
The same user also claims that the compilation contains 82 billion passwords. However, after running our own tests, the actual number turned out to be nearly ten times lower – at 8,459,060,239 unique entries
What measures can save you?
- Finally, as always, make sure to always closely examine all unsolicited spam emails, calls, and text messages for potential phishing activity.
- Most importantly, never click on links or download any executables in messages that you weren't expecting or from senders you don't recognize.
- Use our personal data leak checker and leaked password checker to see if your data has been leaked in this or other breaches.
- If your data has been compromised, make sure to change your passwords across your online accounts.
- You can easily generate complex passwords with our strong password generator or consider using a password manager.
- Enable two-factor authentication (2FA) on all of your online accounts.
It’s time to re-think
"Companies and users need to treat these developments as a wake-up call to end their overblown reliance on passwords," said Veridium's chief revenue officer, Rajiv Pimplaskar. "Passwordless authentication methods such as phone as a token and/or FIDO2 security keys are now commonly available. Such solutions create an un-phishable connection between the user and the IT system and eliminate the need for a password, thereby reducing the attack surface and making the environment more resilient against cyberattacks."
Conclusion
"Any password leaks of large volumes are always alarming to hear and should be taken seriously," said Blue Hexagon CTO and co-founder Saumitra Das. Our own investigation of this report has shown that quite a large number of accounts passwords are recycled from previous breaches and not necessarily active.






