Pegasus Spyware: What Is It? How Does It Infect Your Phone? How Can You Check if Your Phone Has Been Targeted?
Pegasus Spyware is a surveillance software developed and managed by Israel Organisation NSO (Novalpina Omri Shalev). This organization is well known to sell sophisticated software to intelligence agencies, which they build by collecting various vulnerabilities present in smartphone devices. Pegasus is one such software that is created to gain access to your phone without consent and gather personal and sensitive information and deliver it to the user that is spying on you.
Pegasus Spyware: How it can harm you?
Pegasus virus is a Zero-day and Zero-click exploit, so it needs no action from the target person. Initially, we have many Spywares which require some sort of action to be performed at the target side. These actions are clicking on a link, downloading software, etc, but in the case of Pegasus Spyware, the case is different.
According to Kaspersky, Pegasus spyware is able to read the victim's SMS messages and emails, listen to calls, take screenshots, record keystrokes, and access contacts and browser history.
Another report from the Washington post corroborates that hackers can easily hijack every hardware of the victim's devices, hence your device is not your anymore. The hacker can easily gain access to your microphone, camera and can hear and see what you are doing through your device hardware.
Pegasus Spyware: How it infects the device?
The Organized Crime and Corruption Reporting Project (OCCRP) reports that as people as getting more aware of the modern tactics used by malicious code or programs, Zero-Click exploits are the only solution. These exploits are really destructive and dangerous as you won't be able to find that your device has been hacked. This zero-click exploit does not require the victim to even touch his device, it will work automatically and spy every byte of information through your smartphone.
Zero-click exploits rely on bugs in popular apps like iMessage, WhatsApp, and FaceTime, which all receive and sort data, sometimes from unknown sources. Once a vulnerability is found, Pegasus can infiltrate a device using the protocol of the app. The user does not have to click on a link, read a message, or answer a call — they may not even see a missed call or message.
“It hooks into most messaging systems including Gmail, Facebook, WhatsApp, FaceTime, Viber, WeChat, Telegram, Apple's inbuilt messaging and email apps, and others. With a line-up like this, one could spy on almost the entire world population. It's apparent that NSO is offering an intelligence agency as a service,” Timothy Summers, a former cyber engineer at a US intelligence agency said.
The OCCRP reports also point to another method "network injection", which only requires the person to visit an unprotected link during his online activity, once he visited the link, his device will be hijacked by the NSO group software.
Amnesty International recently reported that NSO Group's spyware has infected newer iPhone models, specifically iPhone 11 and iPhone 12, through iMessage zero-click attacks. The spyware can impersonate an application downloaded to an iPhone and transmit itself as push notifications via Apple's servers. Thousands of iPhone handsets have been potentially compromised by the NSO spyware.
Kaspersky states that pegasus spyware does not rely on zero-day vulnerability rather it uses a rooting method called Framaroot. Keep this point, in the case of iOS if the software fails to gain access through Jailbreak, then it breaks the device but in the case of Android, it will ask the user for the permissions it needs to exfiltrate at least some data.
Pegasus Spyware: Can you detect Pegasus Spyware?
Yes, you can detect it, as per reports from Amnesty International, they have developed a tool that will help you to detect the Pegasus Spyware using the Mobile Verification Toolkit (MVT). MVT or Mobile Verification Toolkit works on both Android as well as iOS to detect Pegasus Spyware but it does require some command-line knowledge to operate as of now. There are chances that MVT might receive Graphical User Interface (GUI) in the coming future.
How Can I Protect Myself from This Spyware?
Though there are no exact treatments for Pegasus Spyware, you can take some precautionary steps to avoid any other kind of malware or spyware.
1. Keep your device and applications updated.
It is highly advisable to keep your device and applications up to date as these updates sometimes contain patches and shields against the latest malware. Avoid downloading applications from third-party providers in the form of APK files. These APK files might install some dangerous android applications in your smartphone, which might create a backdoor for some malware.
2. Avoid any unknown and doubtful link
Always have watch on the links where you are tapping. If the URL or the link seems to be doubtful avoid clicking it rather go around way to visit the content if you want, then use any authentic source.
3. Look for privacy indicators
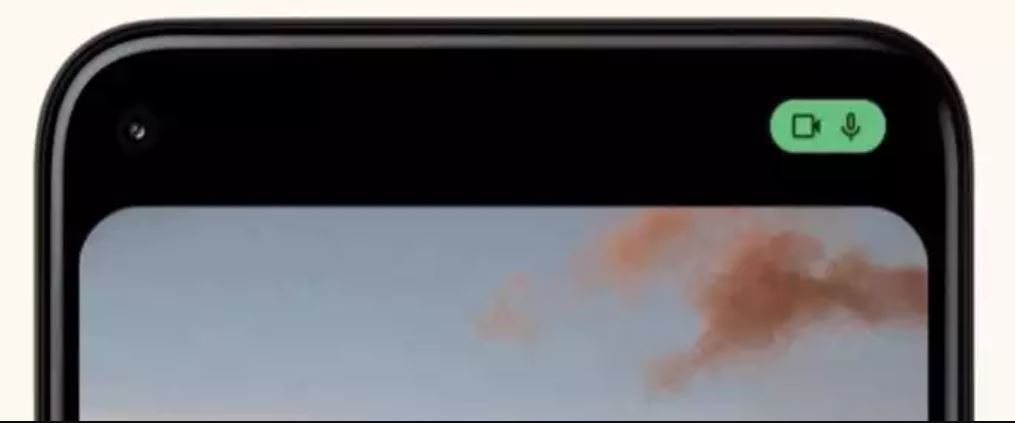
Both Android and iOS are now coming with privacy indicators that will let you know if any application is using your camera or mic in the background. In case you encounter such a situation, and the activity is unknown to your then try to diagnose and find the malicious application and remove it.
FAQ's related to Pegasus Spyware
Q1. What is Zero-Day Exploit?
Zero-Day exploits are those exploits that are not known to the company. Independent researchers find these vulnerabilities but before they inform the company about the bug, their information gets purchased by other groups. This leaves the company a Zero-day plan to react to some attacks. This we have seen with the Windows attack, which let Microsoft release patches for even Windows XP users.
Q2. What is Zero-Click Exploit?
Zero-Click exploits are those exploits that do not require the victim to perform any sort of task such as clicking on a link, downloading a file, installing software, physical access to the victim device, etc.
Q3. Why Pegasus Spyware is Dangerous?
Pegasus Spyware is a Zero-day and Zero-click exploits along with this it acquires the root access of your device and works on kernel level. Kernel-level access gives it full control over your device. In case you find that you as being affected by it, it can self-destruct itself leaving you no clue about the attacker.
Q4. Who uses this Pegasus Spyware?
The NSO group sells these sophisticated software to the government and intelligence so that they can easily spy on someone if they want to.
Q5. What to do if you are affected by Pegasus Spyware?
You cannot do anything if you are affected by Pegasus Spyware. Though you can do one this is, avoid taking your device to a confidential spot or meeting. If you are planning to reset your device, this will work on a temporary basis and you might get affected again very easily.
What is Cryptocurrency? Is it secure?
Related post
"Create the difference and be the change you want to see."
0 comments
Leave a reply
Please Login or Register to Comment. Get StartedWhat is Cryptocurrency? Is it secure?






