Chinese hackers attacked secured Indian govt networks, Tibetan monk’s phone
A compromise was identified in June and July of the Unique Identification Authority of India, or UIDAI, the government agency that oversees the national identification database. A U.S.-based private cybersecurity company said Wednesday, Sept. 22, 2021, it has uncovered evidence that an Indian media conglomerate, a police department and UIDAI.
Chinese authorities have consistently denied any form of state-sponsored hacking and said China itself is a major target of cyberattacks. The allegation has the possibility of increasing friction between the two regional giants, whose relations have already been seriously strained by a border dispute that has led to clashes this year and last year.
What is Cobalt Strike
The charges filed by Sherwin against Chinese citizens for offensive computer intrusions allege that attackers "installed Cobalt Strike malware on Indian government protected computers". Cobalt Strike is a readymade tool that is also used as a penetration testing tool but is often exploited by threat actors. In its report, the Insikt Group suggested the cyberattack could be related to those border tensions.
Amid the controversy of data harvesting by Zhenhua Data, another group of Chinese hackers is in the news for attacking and compromising secured networks and computers belonging to the Indian government last year, court documents filed in the United States have revealed. The Chinese hackers also targeted the phone data of a Tibetan monk in India.
Zhenhua Data
Zhenhua Data, based in the south-eastern Chinese city of Shenzhen, compiled a database relying heavily on public open-source data. Unlike the Zhenhua Data leak, this Chinese attack offensively targeted the database servers by connecting to the Virtual Private Network (VPN) used by the Indian government. The court documents reviewed by India Today suggest that the Chinese attackers used both open market paid malware variants and customised self-developed programs in their operations.
Tibetan monks in India targeted
The charges filed by US prosecutors also reveal that Chinese attackers targeted the phone data of an India-based Tibetan monk in 2019. The Chinese operators used a customised tool called 'SonarX' to store their harvested data. The entries filed in their database showed that the hackers had information about the Indian phone connections used by the Tibetan monk, their chat contents, contacts and usage of digital platforms.
The Attackers
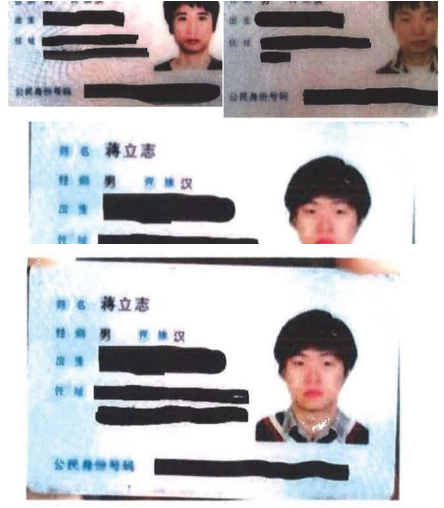
The three top individuals involved in India operations have been identified as Chinese citizens Jiang Lizhi aka Blackfox, Qian Chuan aka Squall and Fu Qiang aka StandNY. All three individuals work for a China-based technology firm called Chengdu 404 Network Technology. Chengdu Technology has been also charged for running multiple computer-operated attacks against several countries, including the US and the UK.
Conclusion
Recorded Future said all victims of the hacks were notified ahead of the publication of the report and provided with its full findings. Most of the data was in the "DNS queries category, which got blocked/dropped at our defense infrastructure," he said in an emailed comment. The company's own investigation of the hack classified the incident as "non-serious alerts and false alarms," he said.






