Android malware spreads by creating automatic replies to messages on WhatsApp
The “wormable” malware, which means that it can spread by itself, could spread further via malicious links and could even extort users by threatening to send sensitive WhatsApp data or conversations to all their contacts.
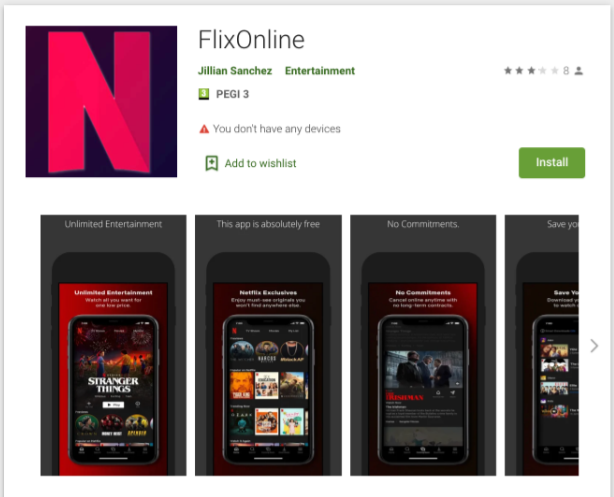
The malware tried to seduce others by offering a free Netflix service by sending the following autoresponder to WhatsApp messages arriving at the victim. “Free 2 Months Netflix Premium Free for Quarantine Reasons (Coronavirus)
The researchers also believe that while the particular app in question was removed from Google Play after it was reported, the malware could return through another similar app in the future. The purpose of obtaining those permissions is believed to allow the malicious app to create new windows on top of other apps, stop the malware from being shut down by the device's battery optimization routine, and gain access to all notifications.
CPR responsibly disclosed the findings to Google. The malicious application was then removed by Google. In the two months, the “Flix Online” app has been downloaded about 500 times. CPR shares the findings with WhatsApp, but there are no vulnerabilities on the WhatsApp site.
Instead of enabling any legitimate service, the FlixOnline app monitors the user's WhatsApp notifications and sends an auto-reply message to all WhatsApp conversations that lures victims with free access to Netflix. The message also contains a link that could allow hackers to gain useful information.
“The malware technique is fairly new and innovative. The technique here is to capture the notifications to hijack the connection to WhatsApp and take predefined actions such as” reject “and” reply “through the notification manager.
“2 Months of Netflix Premium Free at no cost For REASON OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix Premium Free anywhere in the world for 60 days. Get it now HERE https://bit[.]ly/3bDmzUw.”
How malware works
- Victim installs malware from Google’s Play Store
- Malware begins to “listen” for new notifications on WhatsApp
- The malware responds to all WhatsApp messages received by the victim with a response created by the threat actor.
- In this campaign, the response was a fake Netflix site phishing credentials and credit card information.
Security tips for Android users
- Install a security solution on your device
- Download the application only from the official market
- Keep your devices and apps up to date
Conclusion
The fact that the malware was so easily disguised that it could eventually bypass the protection of the Play Store raises some serious danger signals. We have stopped one malware campaign, but the malware family could stay here. The malware can be hidden behind another app and come back.
Data of 500 million LinkedIn users have leaked online
AOW 14: APP OF THE WEEK
Related post
0 comments
Leave a reply
Please Login or Register to Comment. Get StartedAOW 14: APP OF THE WEEK






