Be alert from new Flubot malware
Attacks begin with messages that most commonly claim to come from delivery service DHL – although the names of other brands including Asda, Amazon and Argos are also being leveraged. The Flubot malware can steal user passwords and infect their phones, requiring a factory reset.
These files are usually blocked by default in order to help protect Android users from attacks, but the fake websites provide information on how to bypass these protections and allow FluBot to be installed. FluBot is designed to steal personal information including bank details - and infected users are being exploited to spread the malware to their contacts.
A malware campaign with the aim of stealing passwords, bank details, and other sensitive information is spreading quickly through Android devices. According to the UK’s National Cyber Security Centre (NCSC), users who are infected by the malware must take appropriate steps to protect their data.
They should also ideally change the passwords on any accounts that they may have installed after installing the Flubot virus, according to the NCSC. The company also offers Google Play Protect, a tool to scan for malware, including apps installed outside the Play Store.
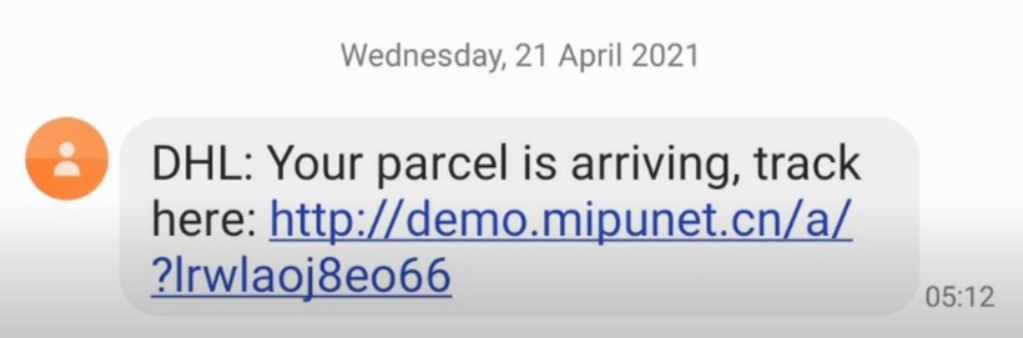
The SMS says that users can track their “missed package delivery” by going to a link in the text message. However, this message is not from DHL.
The Google Play Store is the safest way for users running Google’s Android operating system to install apps and games, thanks in part to the company’s anti-malware protections that scan apps uploaded to the store.
FluBot, temporarily bopped when Spanish police arrested several of the hoods associated with the Android malware early last month, is back, and expanding its geographical reach, Proofpoint reports.
Ways to protect from Flubot
- Well, in that case, you can just call the parcel service and confirm the status of your package or get the tracking number and track the parcel manually from the service provider’s website.
- Moreover, it asks users to format their smartphone/tablet immediately as it is the only way to get rid of the Flubot malware.
- If you receive a suspicious delivery tracking message with a link in it, don’t click on it. That is the best way to save yourself from the Flubot attack. But what if you were going to receive a parcel and the text message is actually from the parcel service.






