Researchers listed the most dangerous malware, viruses Android viruses of 2020
Android Virus is malicious software that contains a set of instruction which is hidden inside the different pirated apps even in Google Play Store. The research shows that there are a number of apps that contain viruses on Google Play Store (between 2016 and early 2020). The virus infected app can do anything depending on its author/hacker objective, a malicious piece of code may force to root your mobile for its author purpose, may conduct a Denial of service (dos) attack, or even breach your private network.
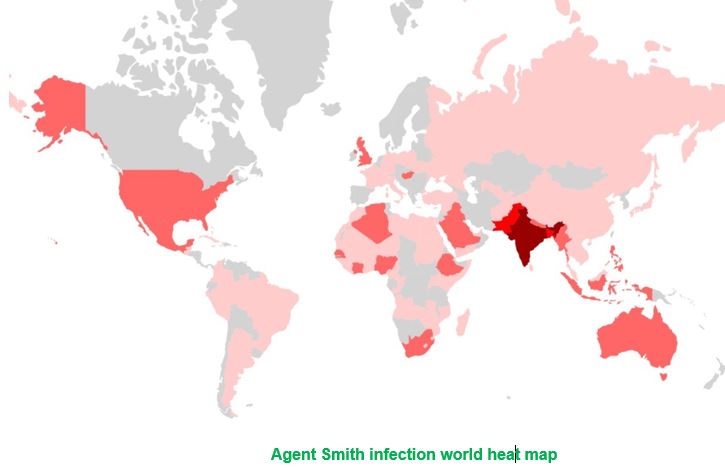
Check Point Research says the Android users should only use trusted app stores to download apps as "third party app stores often lack the security measures required to block adware loaded apps." You can find a technical analysis of the Agent Smith malware on the Check Point blog. A new smartphone malware called "Agent Smith" has been found that has infected 25 million devices worldwide, including 15 million in India, Check Point Research claims. The malware disguises itself as a Google-related application and then replaces installed applications with malicious versions of them using known Android vulnerabilities without users' knowledge.
The list of infected Android apps (malware list)
- JavaTcmdHelper virus
- Com.google.provision
- Com.android.system.ui
- Com.android.gesture.builder
- android.gesture.builder
The virus can be found in applications such as:
- lenovo.anyshare.gps
- mxtech.videoplayer.ad
- jio.jioplay.tv
- jio.media.jiobeats
- jiochat.jiochatapp
- jio.join
- good.gamecollection
- opera.mini.native
- startv.hotstar
- meitu.beautyplusme
- domobile.applock
- touchtype.swiftkey
- flipkart.android
- xender
- eterno
- truecaller
Google's security firewall can still be bypassed
Most of the Android viruses can be downloaded from the Google Play store, together with safely-looking apps. No matter how much effort Google puts while trying to protect users and prevent these malicious apps from bypassing their security, viruses find a way to this store. Security experts reported a list of over 75 applications infected with the Xavier Android virus found on Google Play Store. However, it’s not the only way how Android virus can infect the device.
Be careful when installing third-party apps because they can be infected with the 10001_1.jar virus
1. BLACKROCK Malware
BlackRock malware was first spotted in May. This malware was spotted a few days ago. This malware had stolen information about bank accounts from apps like Gmail, Amazon, Netflix, and Uber. Also, this malware made a total of 337 Android apps as a victim.
2. FAKESKY malware
FAKSKY is one of the world's most dangerous malware. This malware has made a comeback after three years and through this hackers are not only stealing users' personal data but are also trying to empty their bank accounts.
3. The EventBot malware
event bot targeted Indian users in May this year. Experts say that the hackers tried to hack the banking app, money transfer service, and cryptocurrency wallet through this malware.
4. AGENT SMITH Malware
Agent Smith is one of the dangerous malware. This malware targeted 25 million Android users last year, including 15 million Indian users. Let us know that this malware came as a Google-related app.
5. ExoBot
ExoBot, is a banking malware updated version is using three hazardous components in one campaign: malware, credential phishing, and banking data theft. Security experts warn that this version of Android malware is more complicated and difficult
Once it comes never return
Once installed, a malicious app creates a legit-looking icon on the home screen that looks similar to Bank Austria. After installing the Marcher virus, victims are asked to enter their credit card information or other personally identifiable details whenever they open any applications.

6. NotCompatible virus
NotCompatible virus is a dangerous Android virus that acts as a proxy. As soon as it gets into its target system, it connects to its server and waits for specific commands. There have been many speculations that this malware is capable of connecting affected devices into a botnet and then turning them into spam machines.
Some part of security experts has warned that NotCompatible malware can easily be used to steal personal information from the phone or similar device. To protect yourself from these issues, we highly recommend you to download mobile antivirus. It will help you to prevent the infiltration of such and similar threats.
7. Lastacloud virus
Lastacloud virus is a trojan horse also known as Android. Lastacloud. It has been actively spread as updates for WhatsApp and Android Browser that present themselves as Updatecom.whatsapp.update and com.androidbrowser.update.
8. Android Police virus
Android Police Virus is a newly-designed version of the FBI virus, which is capable of infecting Android OS. Today, it is the most dangerous example of the Android virus because it can block the entire system and encrypt each of the files that are installed on it.
9. Android ransomware
Android ransomware is a malicious mobile phone threat that uses a clickjacking technique to get admin rights on the victimized Android device. However, it can also infiltrate the device through malicious apps, such as Porn ‘O’ Mania.
10. Svpeng virus
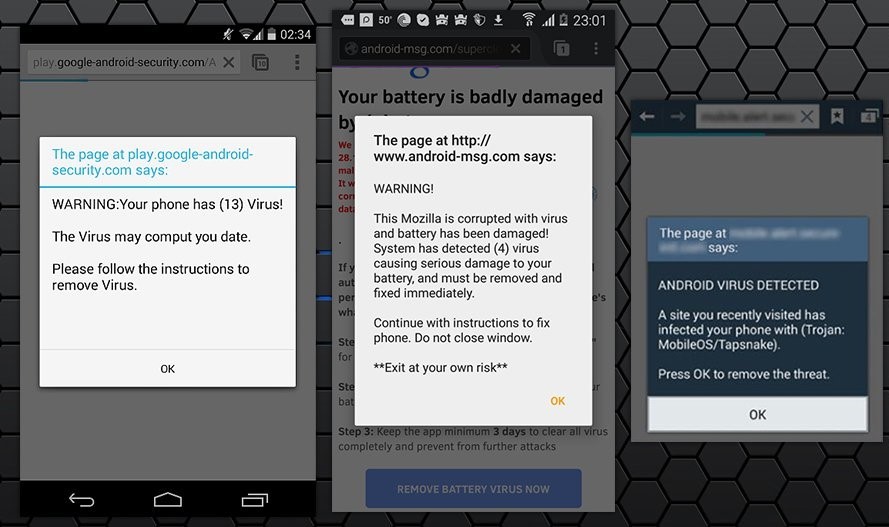
It is a typical “lock screen” parasite that blocks the screen of the phone with a fake warning message from the FBI. In reality, people who are working behind Svpeng ransomware do not have any connections to the FBI. They are seeking just to trick their victims into paying the fake ransom. Please, do NOT fall for these claims. You need to remove Svpeng from the system by resetting your Android device to factory settings.
11. Mazar malware
Typically, it starts monitoring the phone or another Android device, changes its settings according to its needs, sends SMS to premium numbers, and initiates illegal connections via the Internet. Those who are connected to are granted with administrator rights, so they can do whatever they want.
12. Ghost Push virus
Ghost Push virus is a notorious Android malware that is capable of infecting all Android devices that are using versions below Nougat (V7). The malicious actor functions as a rootkit – it is capable of performing various malicious activities without users' permission. Unfortunately, getting rid of Ghost Push is almost impossible, even factory reset does not do the job, and reflashing firmware would be the only choice for users.
13. Gooligan malware
Gooligan malware has corrupted over 86 applications, such as Youtube Downloader, Kiss Browser, Memory booster, Demo, Perfect Cleaner, Battery Monitor, System Booster, etc. It seems that all system performance and browser-related programs and gaming, as well as pornographic applications, risk becoming the carriers of Gooligan.
After the infection process is complete, the malware roots the device and enables full access to install more malicious elements.
14. HummingWhale virus
HummingWhale malware was apparently available on Google Play Store for a while in the form of 20 various applications, most of them being called [random word] Camera. Examples include Rainbow Camera, Whale Camera, Ice Camera, Hot Camera, and similar applications.
The malware used to set up a virtual machine on the infected device, stealthily install extra applications on the device and serve annoying advertisements for the user.
15. HummingBad virus
First discovered in February 2016, malware has already infected more than 10 million Android users. The malware had been spreading via “drive-by download attacks, ” and users got infected after visiting particular malicious websites. Malware also gets full access to the infected device and can steal users’ private information, such as contacts, logins, credit card, or banking information. For this reason, it’s crucial to remove HummingBad as soon as it shows up on the device.
16. Lockdroid ransomware
Lockdroid ransomware, also known as Android.Lockdroid.E spreads as a pornography app “Porn ‘O’ Mania”. The virus uses social engineering techniques to get the admin rights of the infected device. It aims to achieve this goal by using a fake package installation. As soon as the installation is completed, the Lockdroid virus gets full access to the device and encrypts data. What is more, it can change the PIN and lock the device. In this way, malware elimination might become difficult. Malware uses the clickjacking technique and attacks smartphones and tablets with Android 5.0 or newer versions of the OS. According to Google, this malicious app cannot be downloaded from the Google Play Store.
17. GhostCtrl virus
GhostCtrl virus exploits an Android vulnerability to help its owners to get control over the device. It showed up in the middle of 2017 when it was found attacking Israeli hospitals, but it is not considered a new virus. It spreads presenting itself as a legitimate app, such as WhatsApp and Pokemon Go. Once inside the system, GhostCtrl malware drops a malicious Android application package (APK) and opens the backdoor of the system to provide full access to the victim's personal information, videos, and audios
18. Invisible Man
The virus spreads as a fake Flash Player app in the suspicious and insecure download websites. Fortunately, malware hasn't made it to the Google Play Store. However, when users install this malicious app, they give administrator rights to the device. As a result, cybercriminals can control it via the Command and Control server.
19. LeakerLocker ransomware virus
LeakerLocker ransomware virus. In the middle of August 2017, malware researchers discovered LeakerLocker spreading via two apps available on Google Play Store. The malicious application was hiding under Wallpapers Blur HD” and “Booster & Cleaner Pro” apps. One user's installed one of these programs, the malware locks the device's screen with a threatening message.
20. DoubleLocker ransomware virus
DoubleLocker ransomware virus. In September 2017, malware researchers spotted a new version of mobile malware. It spreads as a fake Adobe Flash update. After the attack, it locks the device by replacing the PIN. Then it launches data encryption and demands to pay 0.0130 Bitcoins to unlock the device and recover files. Additionally, malware might also steal money from PayPal and banking accounts. Therefore, removal of the virus should be performed ASAP. However, non-routed device owners might need to factory-reset infected phones to unlock them. Routed device users can use the Android Debug Bridge (ADB) tool. Further, DoubleLocker removal has to be completed with security software.
21. LokiBot virus
Infostealer.Lokibot is a malicious application designed for Android smartphones. Once it gets on the victim's device, it becomes capable of sending SMS messages and replying to them, use mobile browsers, address particular URLs and install the SOCKS5 proxy. As a result, the victim's outgoing traffic can be redirected. The virus can also compose and display fake notifications for the user, prompting the victim to open a bank account
22. Tizi Android virus
The virus works as spyware and is designed to steal personal information from social media apps, including Facebook, LinkedIn, Skype, WhatsApp, etc. Malware might also record calls, access SMS, take pictures, and complete many other tasks that put Android user's privacy at risk.Tizi virus might also get root access by exploiting system vulnerabilities or tricking a user into giving such permission during the installation of a malicious app.
23. Anubiscrypt ransomware
ESET security researcher spotted the virus on Google Play. The threat is not only capable of encrypting all pictures, videos, music, and other personal files, but also permanently locking the phone screen, preventing its access.
Besides that, Anubis malware is also can perform the following on the host device:
- Steal victims' PayPal, eBay, Amazon, and other credentials;
- Intercept SMS;
- Log all keystrokes;
- Grant remote access to hackers.
24. Opt-Out virus
The opt-out virus is one of those pesky Android infections that users simply can't get rid of, and some are even forced to perform a factory reset. Users reported that, seemingly out of nowhere, they started receiving pop-ups, interstitial, auto-play, and other annoying ads. To make matters worse, these notifications are often hindering the background of the display, and show up over all other apps, as well as the user interface (UI) components such as a keyboard. If the marking is clicked, users are redirected to a rogue optout.tracker.ared.re/opt-out/mobile= URL, where they are asked to download another suspicious application. Please do not download anything that Opt-out virus suggests, as you might infect your android with more adware or even malware.
Mobile devices are intricate systems nowadays with thousands of different configuration settings, app permissions, and other peculiarities – it is very easy to get lost when dealing with such threats like the Opt-Out virus. To get rid of it, users should determine which app is causing suspicious ads, although sometimes it might be more difficult than it seems. In most cases, the culprit is coming from a third-party site, so in case you recently downloaded something from such sites, uninstall it immediately.
Additionally, you could also go to Settings > Apps > Advanced/three dots at the top-right of the screen > Special app access > Display over other apps, and check which apps have the permission to display over other applications and the US components.
Apple probably bring single-band 5G in iPhone 13 by 2021
Top 8 COVID-19 gadgets
Related post
0 comments
Leave a reply
Please Login or Register to Comment. Get StartedTop 8 COVID-19 gadgets






