Ripple20 bug: Millions of IoT Devices at Risk
An Israel based security firm, JSOF on Tuesday, revealed a collection of critical vulnerabilities which were given the name 'Ripple20', a total of 19 hackable bugs it has identified in a widely used Transmission Control Protocol/Internet Protocol (TCP/IP) software library developed by an Ohio-based software company Treck which is a provider of software used in Internet-of-Things devices. These loopholes were detected through an extensive analysis of over many months.
Ripple20 affected a diverse group of vendors, including HP, Intel, Rockwell Automation, Schneider Electric, Caterpillar, Baxter, as well as many other major international vendors suspected of being of vulnerable in medical, transportation, industrial control, and other industries.
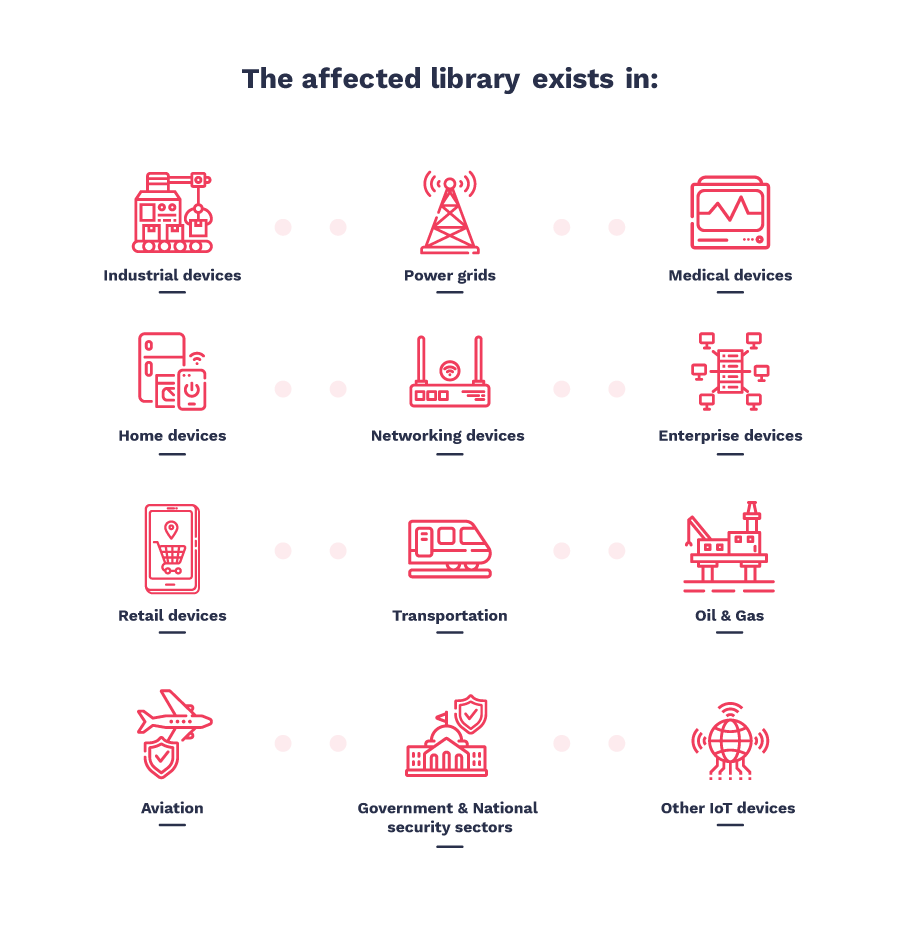
The devices that are affected by these security loopholes are ranging from power supply systems in data centres, programmable logic controller in industries, and medical industries etc.
JSOF has also demonstrated the exploitation of these Vulnerabilities on different devices as a proof-of-concept.
As reported by the JSOF lab researchers, four of these Ripple20 vulnerabilities are rated critical, with CVSS scores over 9 and enable Remote Code Execution. The other 15 vulnerabilities are in the range of 3.1 to 8.2 CVSS score, and effects ranging from Denial of Service(DoS) to potential Remote Code Execution.
Risk Evaluation-
- An attacker outside the network can take control over devices connected within the network.
- Specific devices within the network can be targeted if the attacker has already infiltrated in.
- An attacker may use the affected device to remain hidden within the network for years.
- An attacker could broadcast an attack capable of taking control over all the devices connected through the network simultaneously.
These vulnerabilities are unique both in their widespread effect and impact due to supply chain effect. These Ripple20 vulnerabilities allow the attackers to bypass the NAT and firewall and take control over devices undetected, with no user interaction required. This is due to the vulnerabilities being low in TCP/IP stack. This allows the attacker to pass as legitimate traffic.
JSOF has reported these issues to Treck who have in return replied positively and collaborated with JSOF researchers in getting the issues fixed. The affected clients like HP, Intel, Schneider Electric and Rockwell Automation etc have all acknowledged these critical vulnerabilities.
You can find out more about this here.






